
Your users are the weakest link in defending against cybercrime like phishing.They need to stay informed about the latest phishing threats and how to avoid becoming a victim to keep themselves and your organization safe.
Get the tools and information you need to stay one step ahead of cybercriminals
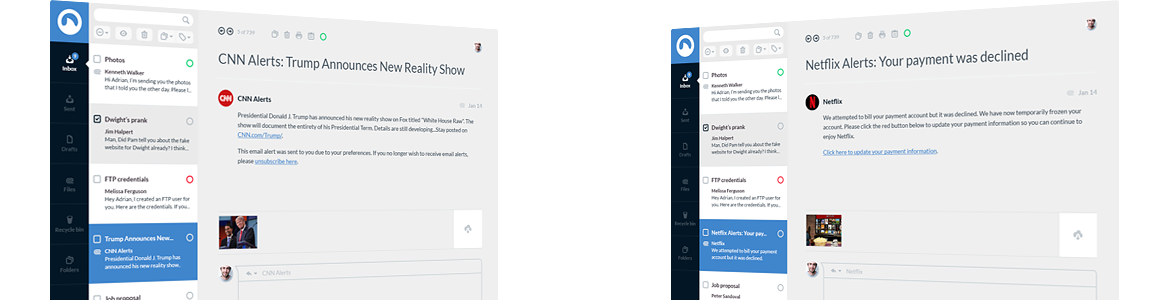
Give your users a safe way to report phishing emails to IT in a single click with KnowBe4's Phish Alert Button.
Find out now how many of your users are phish prone with KnowBe4's free phishing security test.
Get more in-depth knowledge about why phishing is successful and what you can do to stop it at your organization.
Want to learn more about how phishing can affect you or your business? Here are the latest news articles:
© KnowBe4, Inc. All rights reserved. | Privacy Policy & Terms Of Service